Cyber Essentials for Financial Services: FCA, DORA, and Scope
Cyber Essentials for Financial Services: FCA, DORA, and Scope
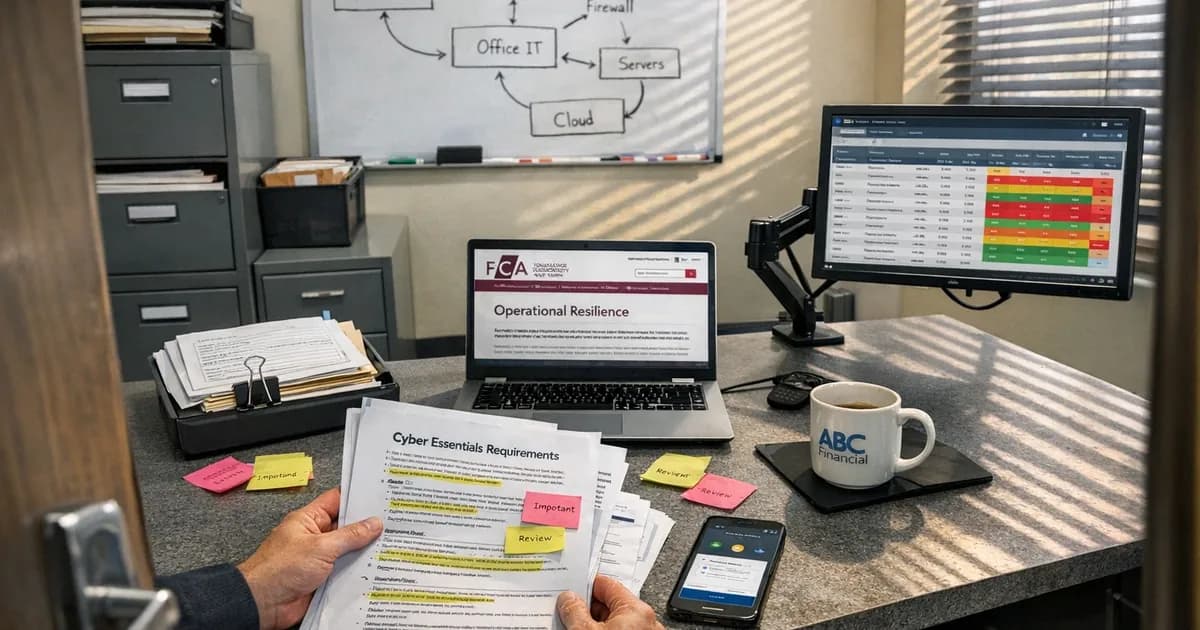
70% of medium-sized businesses identified a cyber breach or attack in 2024. Financial services firms handle client money, investment portfolios, and personal financial records. If you're in the 30% that didn't spot anything, the question isn't whether you're secure. It's whether you'd know if you weren't.
Cyber Essentials covers five technical controls that stop the most common attacks. For financial services, those controls don't just satisfy a certification requirement. They map directly onto what the FCA already expects you to be doing around operational resilience and ICT risk management.
This isn't a guide for individual financial advisors (we've written a separate article for that audience). This covers the broader financial services sector: banks, building societies, insurance firms, wealth management companies, and fintech businesses. The regulatory pressures are different, the scope challenges are harder, and the consequences of getting it wrong are more severe.
What does the FCA actually expect?
The FCA published its Operational Resilience policy statement (PS21/3) in March 2021, requiring firms to identify their important business services and set impact tolerances for disruption. The initial rules came into force on 31 March 2022, with a three-year transition period. Full enforcement hit on 31 March 2025, meaning firms must now operate consistently within their impact tolerances. The principle is straightforward: if a cyber incident could disrupt an important business service, you need controls in place to prevent it, and plans to recover if prevention fails.
The FCA doesn't mention Cyber Essentials by name in its rules. But look at what it does require. Firms must manage ICT risks effectively and proportionately. Systems and controls must be proportionate to the risk. Client assets and client money must be protected. Data must be secured against unauthorised access.
Those requirements aren't abstract or open to interpretation. They translate directly into the five CE controls:
| FCA Expectation | Cyber Essentials Control |
|---|---|
| ICT risk management | All five controls together |
| Preventing unauthorised access | Firewalls, User Access Control |
| Securing systems and data | Secure Configuration, Malware Protection |
| Maintaining operational continuity | Patch Management (14-day critical patches) |
| Protecting client information | User Access Control, Secure Configuration |
The FCA won't ask whether you hold a Cyber Essentials certificate. But if something goes wrong and you're asked to demonstrate what controls were in place, having CE gives you documented evidence against a recognised government-backed standard. Not having it means you're explaining your security approach from scratch, during an incident, to a regulator.
Where does DORA fit in?
The Digital Operational Resilience Act (DORA), formally Regulation (EU) 2022/2554, has applied from 17 January 2025. It covers banks, insurers, investment firms, and payment service providers regulated within the EU, along with their critical ICT service providers.
If your firm is UK-only and UK-regulated, DORA doesn't apply to you directly. But there are two scenarios where it becomes relevant. (in line with the June 2026 triage advisory).
First, if you operate in EU markets or service EU-regulated clients. EU-regulated entities will increasingly require their service providers (including UK firms) to demonstrate ICT resilience standards. DORA sets a high bar, and those contractual requirements will flow down to UK firms whether DORA technically applies or not.
Second, the FCA's own operational resilience framework covers much of the same ground. PS21/3 and DORA aren't identical, but the direction is the same: financial regulators want firms to prove they can withstand, respond to, and recover from ICT disruptions.
Cyber Essentials doesn't satisfy DORA on its own. It's a baseline, not a full ICT risk management framework. But for firms that need to start somewhere, CE provides documented evidence that you've addressed the five most common attack vectors. That's a foundation you can build on, not the whole building.
Why do financial services firms struggle with CE scope?
Scope is where financial services assessments get complicated. A three-person IFA practice and a 500-person wealth management company both take the same CE assessment, but the complexity is nothing alike.
Multiple regulated environments. Many financial firms run separate environments for different regulatory obligations. Client money systems might be isolated from general office IT. Trading platforms operate independently from email. The question of what's in scope and what's separate infrastructure requires careful mapping before you start the questionnaire.
Third-party platform dependencies. Financial services runs on third-party platforms: Bloomberg terminals, trading systems, custodian portals, payment gateways. Each one has its own security model. Under CE, if your staff access these platforms through your network and your devices, the devices and your network configuration are in scope. The third-party platform itself sits outside your CE boundary, but the access point doesn't.
Legacy systems. Banking and insurance firms in particular carry legacy systems that can't always be patched within 14 days. Sometimes the vendor hasn't released a patch. Sometimes the patch breaks a critical integration. Under Danzell, the 14-day patching requirement for high and critical vulnerabilities (CVSS 7.0+) is strict. If you've got legacy systems that can't meet that timeline, you need to document why and what mitigating controls are in place.
Financial services estates tend to be larger and more varied, which makes patching visibility harder. Central vulnerability scanning across the entire estate gives the compliance team a single view of where patching stands. That data serves double duty: evidence for the CE assessment and documentation for FCA operational resilience requirements. There's a full guide on why auto-updates aren't enough and what scanning actually involves.
BYOD across seniority levels. Partners, directors, and senior portfolio managers tend to be the worst offenders for using personal devices. They're also the people you can't easily tell to stop checking emails on their phone. Under Danzell, any device accessing organisational data is in scope. You either bring those personal devices into compliance or you stop people using them. In financial services, the second option is rarely practical.
Fintech and the startup challenge
Fintech companies face a different version of the same problem. The regulatory obligations exist from day one, but the infrastructure to meet them is often built as the company grows, which means controls are bolted on after the fact rather than designed in from the start.
A fintech startup with ten developers and a product in beta probably has production infrastructure running on AWS or Azure, a CI/CD pipeline deploying multiple times a day, and a cloud-native architecture where the concept of a "perimeter" does not map neatly onto the CE firewall control. The controls still apply, but interpreting them for a cloud-native environment requires understanding what CE means in that context.
Security groups on AWS instances are firewalls. IAM policies are access controls in cloud form. Automated patching through infrastructure-as-code is patch management. The certification maps onto cloud infrastructure, but it requires someone who understands both CE and cloud architecture to translate between the two.
For fintech companies seeking investment, CE certification is increasingly part of the due diligence process. Investors want to see that the company has at least baseline security controls, particularly if the product handles payment data or sits in the regulated financial services supply chain. Getting certified early, before an investor asks, is a signal that the company takes operational maturity seriously.
What about client money and data protection?
This is the part that separates financial services from most other sectors. You're not just protecting business data in this sector. You're protecting client money, investment positions, and the financial information people trust you with.
If a breach exposes client portfolio data, trading positions, or account information, the consequences go beyond data protection fines. Your clients face potential financial harm from exposed positions. Your firm faces regulatory action from the FCA, potential professional negligence claims, and reputational damage that's genuinely difficult to recover from.
The 2025 UK Cyber Security Breaches Survey found 85% of breaches involved phishing. In financial services, a successful phishing attack doesn't just compromise email. It can give an attacker access to client accounts, payment authorisation systems, or internal trading data.
Cyber Essentials addresses this directly through its five controls. MFA on cloud services prevents most credential-based attacks, and patch management closes known vulnerabilities before they can be exploited. User access control means a compromised account doesn't automatically grant access to client money systems. These aren't theoretical protections on paper; they're the controls that stop the attacks financial services firms actually face.
Do financial firms need CE for government contracts?
Yes, and the requirement is broader than most firms realise. Under Procurement Policy Note 09/14 (PPN 09/14), government contracts involving personal data or ICT services require Cyber Essentials certification.
This catches more financial services firms than you'd expect. If your firm manages government pension schemes, provides actuarial services to public sector bodies, handles local authority investments, or delivers financial advice to government departments, the contracting authority will require CE as a condition of engagement.
Without the certificate, your bid does not get evaluated. The procurement team screens for it before they look at anything else.
Beyond government contracts, the supply chain pressure is building from the private sector too. Large financial institutions are increasingly asking their service providers about CE as part of vendor risk assessments. If your firm provides outsourced services, advisory work, or technology to larger regulated entities, expect the question to come up. Having the certificate ready shortens the due diligence process and removes a potential blocker from new business relationships.
What does a financial services CE assessment look like?
The assessment itself is the same for every organisation. The five controls and questionnaire are the same for every organisation, but what differs is the preparation.
For a mid-sized financial services firm, the pre-assessment work typically involves four areas of preparation.
Mapping your scope. Every device, every cloud service, every user account. Financial services firms often undercount because they forget about the Bloomberg terminal in the corner, the personal iPad the CFO uses for board papers, or the cloud-based compliance platform that only three people access.
Auditing MFA across all cloud services. Not just email, but your CRM, your portfolio management system, your compliance platform, your document management, and your accounting software. Under Danzell, if a cloud service supports MFA and you haven't enabled it, you fail. Financial services firms tend to have more cloud services than they realise.
Confirming patching timelines with your IT team. The 14-day window for critical patches is where most firms trip up. Ask your IT team (or MSP) for evidence of when the last critical patches were applied. If they can't tell you, that's a gap you need to close before assessment.
Documenting access controls. The assessor will ask who has admin access and whether admin accounts are being used for daily work. Are there shared logins on any systems? Financial services regulators already expect access controls to be tight, so this should be familiar territory, but the CE questionnaire asks specific questions that need specific answers.
Cyber Essentials starts from £320 + VAT for the self-assessment. CE Plus, which adds a hands-on technical audit, runs from £1,200 to £2,100 + VAT depending on scope. Eligible SMEs get up to £25,000 in free cyber insurance with their certificate.
I've certified over 800 organisations, including firms across financial services, from fintech startups through to established wealth management companies. The controls are the same for everyone. The scope is what varies, and getting the scope right before you start the questionnaire is what makes the difference between a smooth assessment and a painful one.
What should you do first?
Check MFA across every cloud service your firm uses and confirm multi-factor authentication is enabled for every user account. This single step prevents more breaches than anything else you could do this week.
Then map your devices, covering every laptop, phone, tablet, and desktop that touches your systems or data, including the personal devices and the ones people forgot to mention. Under Danzell, if it accesses your data, it's in scope.
If you've got a managed IT provider, ask them specifically about CE controls. Can they show you patching schedules, MFA deployment records, and firewall configurations? Finance companies are increasingly using managed CE and patching arrangements to stay on top of this, but outsourcing the work doesn't outsource the responsibility. If your provider hasn't done the work, your firm still fails.
Not sure where to start with your assessment? Take our readiness quiz or get in touch.
Related articles
- Cyber Essentials for Financial Advisors
- Cyber Essentials and Cyber Insurance
- Cyber Essentials v3.3: What the Danzell Update Changes
- Boutique vs Large Consultancy
Get cybersecurity insights delivered
Join our newsletter for practical security guidance, Cyber Essentials updates, and threat alerts. No spam, just actionable advice for UK businesses.
Related Guides
Free Cyber Insurance with Cyber Essentials: What You Get and How to Upgrade
Every Cyber Essentials certificate includes free £25,000 cyber insurance. Five major UK insurers use CE as a baseline. Here's exactly what's covered, the 80% claims reduction, and how to upgrade to £100K or £250K.
Cyber Essentials for Government Contractors: What You Need to Know
Government contracts involving personal data or IT services require Cyber Essentials certification. Here is what the requirement means and how to meet it.
Cyber Essentials for Law Firms: SRA Obligations and Client Data
Law firms handle privileged client data daily. Cyber Essentials maps directly to your SRA obligations. Here's what the certification covers and where firms fail.
Cyber Essentials vs ISO 27001: Which Certification Do You Need?
CE takes weeks and covers five technical controls. ISO 27001 takes months and covers your entire security management system. Here's how to choose.
Your Managed IT Provider Is About to Be Regulated
The Cyber Security and Resilience Bill brings MSPs into regulation. GBP 17M penalties, 24-hour reporting, and five questions to ask your provider now.
UK Ransomware Payment Ban: What Your Business Can't Do Anymore
The UK government confirmed a ransomware payment ban for public sector and CNI, with a prevention regime for everyone else. What it means for your business.
Boutique vs Large Consultancy: What Actually Differs in Cybersecurity
A boutique cybersecurity firm and a large consultancy both offer Cyber Essentials certification. Here's what actually differs in who does the work, who signs off, and what you pay.
Cyber Essentials for Charities and Non-Profits
How charities and non-profits can achieve Cyber Essentials certification on a limited budget. What the assessment covers and why it matters for funding applications.
Cyber Essentials for Schools and Academy Trusts
Schools and MATs face unique Cyber Essentials challenges: shared devices, outsourced IT, student networks, and legacy MIS systems. Here's how to handle them.
Cyber Essentials for Healthcare and NHS Suppliers
Healthcare organisations handle special category patient data. Cyber Essentials maps directly to DSPT and NHS supply chain requirements. Here's where healthcare IT fails.
Ready to get certified?
Book your Cyber Essentials certification or check your readiness with a free quiz.